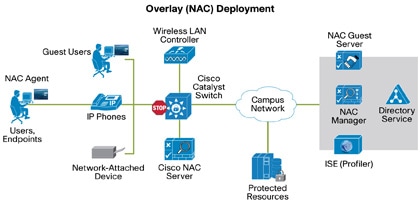
- Cisco Systems has launched the Self-Defending Network Initiative (SDNI) to dramatically improve the network's capability to identify, prevent, and adapt to threats. A key part of this initiative is Network Admission Control (NAC). NAC is a multipart solution that validates the security posture of the endpoint before admitting it on the network.
- Network Access Control (NAC) helps enterprises implement policies for controlling devices and user access to their networks. NAC can set policies for resource, role, device and location-based.
- When autocomplete results are available use up and down arrows to review and enter to select.
- Cisco Network Admission Control Agent Software For Mac Osx
- Cisco Network Admission Control Agent Software For Mac 2017
- Cisco Network Admission Control Agent Software For Mac Download
Cisco's Network Magic was a versatile, feature-rich tool with a wide range of utilities, and it afforded users surprising levels of convenience. It was compatible with both Mac OS and Windows. It came in a free version, known as Network Magic Essentials, and a small business edition called Network Magic Pro.
Register your product to gain access to bonus material or receive a coupon.
- By Jazib Frahim, Omar Santos, David C. White
- Published Nov 21, 2006 by Cisco Press. Part of the Networking Technology series.
eBook (Watermarked)
- Your Price: $38.40
- List Price: $48.00
This PDF will be accessible from your Account page after purchase and requires the free Adobe® Reader® software to read it.
The eBook requires no passwords or activation to read. We customize your eBook by discreetly watermarking it with your name, making it uniquely yours.
- Copyright 2007
- Dimensions: 7-3/8' x 9-1/8'
- Edition: 1st
- eBook (Watermarked)
- ISBN-10: 1-58705-403-5
- ISBN-13: 978-1-58705-403-7
Cisco Network Admission Control
Volume II: NAC Framework Deployment and Troubleshooting
The self-defending network in action
Jazib Frahim, CCIE® No. 5459
Omar Santos
David White, Jr., CCIE No. 12,021
When most information security professionals think about threats to their networks, they think about the threat of attackers from the outside. However, in recent years the number of computer security incidents occurring from trusted users within a company has equaled those occurring from external threats. The difference is, external threats are fairly well understood and almost all companies utilize tools and technology to protect against those threats. In contrast, the threats from internal trusted employees or partners are often overlooked and much more difficult to protect against.
Network Admission Control (NAC) is designed to prohibit or restrict access to the secured internal network from devices with a diminished security posture until they are patched or updated to meet the minimum corporate security requirements. A fundamental component of the Cisco® Self-Defending Network Initiative, NAC enables you to enforce host patch policies and to regulate network access permissions for noncompliant, vulnerable systems.
Cisco Network Admission Control, Volume II, helps you understand how to deploy the NAC Framework solution and ultimately build a self-defending network. The book focuses on the key components that make up the NAC Framework, showing how you can successfully deploy and troubleshoot each component and the overall solution. Emphasis is placed on real-world deployment scenarios, and the book walks you step by step through individual component configurations. Along the way, the authors call out best practices and tell you which mistakes to avoid. Component-level and solution-level troubleshooting techniques are also presented. Three full-deployment scenarios walk you through application of NAC in a small business, medium-sized organization, and large enterprise.
'To successfully deploy and troubleshoot the Cisco NAC solution requires thoughtful builds and design of NAC in branch, campus, and enterprise topologies. It requires a practical and methodical view towards building layered security and management with troubleshooting, auditing, and monitoring capabilities.'
–Jayshree V. Ullal, Senior Vice President, Datacenter, Switching and Security Technology Group, Cisco Systems®
Jazib Frahim, CCIE® No. 5459, is a senior network security engineer in the Worldwide Security Services Practice of the Cisco Advanced Services for Network Security team. He is responsible for guiding customers in the design and implementation of their networks with a focus on network security.
Omar Santos is a senior network security engineer in the Worldwide Security Services Practice of the Cisco Advanced Services for Network Security team. He has more than 12 years of experience in secure data communications.
David White, Jr., CCIE No. 12,021, has more than 10 years of networking experience with a focus on network security. He is currently an escalation engineer in the Cisco TAC, where he has been for more than six years.
- Effectively deploy the Cisco Trust Agent
- Configure Layer 2 IP and Layer 2 802.1x NAC on network access devices
- Examine packet flow in a Cisco IOS NAD when NAC is enabled, and configure Layer 3 NAC on the NAD
- Monitor remote access VPN tunnels
- Configure and troubleshoot NAC on the Cisco ASA and PIX security appliances
- Install and configure Cisco Secure Access Control Server (ACS) for NAC
- Install the Cisco Security Agent Manage-ment Center and create agent kits
- Add antivirus policy servers to ACS for external antivirus posture validation
- Understand and apply audit servers to your NAC solution
- Use remediation servers to automatically patch end hosts to bring them in compliance with your network policies
- Monitor the NAC solution using the Cisco Security Monitoring, Analysis, and Response System (MARS)
This security book is part of the Cisco Press® Networking Technology Series. Security titles from Cisco Press help networking professionals secure critical data and resources, prevent and mitigate network attacks, and build end-to-end self-defending networks.
Category: Cisco Press–Security
Covers: Network Admission Control
Table of Contents
Introduction
Part I NAC Overview
Chapter 1 NAC Solution and Technology Overview
Network Admission Control
NAC: Phase I
NAC: Phase II
NAC Program Participants
Components That Make Up the NAC Framework Solution
Cisco Trust Agent
Cisco Security Agent
Network-Access Devices
Cisco VPN 3000 Series Concentrator
Cisco Secure Access Control Server
Event Monitoring, Analysis, and Reporting
Summary
Review Questions
Part II Configuration Guidelines
Chapter 2 Cisco Trust Agent
Preparing for Deployment of CTA
Supported Operating Systems
Deploying CTA in a Lab Environment
CTA Windows Installation
CTA Windows Installation with the 802.1X Wired Supplicant
CTA Mac Installation
CTA Linux Installation
Installing the CA Certificate
User Notifications
Customizing CTA with the Optional ctad.ini File
[main] Section
[EAPoUDP] Section
[UserNotifies] Section
[ServerCertDNVerification] Distinguished Name-Matching Section
[Scripting_Interface] Section
Example ctad.ini
CTA Scripting Interface
Requirements for Using the Scripting Interface
Executing the Scripting Interface
CTA Logging Service
Creating a ctalogd.ini File
Using the clogcli Utility
Deploying CTA in a Production Network
Deploying CTA on Windows
Deploying CTA on Mac OS X
Deploying CTA on Linux
Troubleshooting CTA
Installation Issues
Communication Issues
System Logs
CTA Client Fails to Receive a Posture Token
CTA 802.1X Wired Client
Client Is Disconnected (Suspended)
Chapter Summary
References
Review Question
Chapter 3 Cisco Secure Services Client
Installing and Configuring the Cisco Secure Services Client
Minimum System Requirements
Installing the Cisco Secure Services Administrative Client
Configuring the Cisco Secure Services Administrative Client
Deploying the Cisco Secure Services Client in a Production Network
End-User Client Deployment Installation Prerequisite
Creating End-User Client-Configuration Files
Creating the License File
Deploying the End-User Client
Viewing the Current Status of the Cisco Secure Services Client
Windows Wireless Zero Configuration
Troubleshooting the Cisco Secure Services Client
System Report Utility
Viewing the Client Logs and Connection Status in Real Time
Client Icon Does Not Appear in System Tray
Client GUI Does Not Start
Client Does Not Prompt for Password
Wireless Client Is Immediately Dissociated after 802.1X Authentication
Client Is Disconnected (Suspended)
Summary
References
Review Question
Chapter 4 Configuring Layer 2 NAC on Network Access Devices
NAC-L2-IP
Architecture of NAC-L2-IP
Configuring NAC-L2-IP
Troubleshooting NAC-L2-IP
NAC-L2-802.1X
Architecture of NAC-L2-802.1X
Configuring NAC-L2-802.1X
MAC Authentication Bypass
Troubleshooting NAC-L2-802.1X
Configuring NAC-L2-802.1X on Cisco Wireless Access Points
Summary
Review Questions
Chapter 5 Configuring Layer 3 NAC on Network Access Devices
Architectural Overview of NAC on Layer 3 Devices
Configuration Steps of NAC on Layer 3 Devices
Step 1: Configuring AAA Authentication
Step 2: Defining the RADIUS Server
Step 3: Specifying the Interface Access Control List
Step 4: Configuring the NAC Parameters
Step 5: Defining the NAC Intercept Access Control List (Optional)
Step 6: Setting Up the Exception Policies (Optional)
Step 7: Configuring the Clientless Host Parameters (Optional)
Step 8: Optimizing the NAC Parameters (Optional)
Monitoring and Troubleshooting NAC on Layer 3 Devices
Useful Monitoring Commands
Troubleshooting NAC
Summary
Review Questions
Chapter 6 Configuring NAC on Cisco VPN 3000 Series Concentrators
Architectural Overview of NAC on Cisco VPN 3000 Concentrators
Cisco Software Clients
Microsoft L2TP over IPSec Clients
Configuration Steps of NAC on Cisco VPN 3000 Concentrators
VPN Configuration on the VPN 3000 Concentrator
VPN Configuration on the Cisco VPN Client
NAC Configuration on the VPN 3000 Concentrator
Testing, Monitoring, and Troubleshooting NAC on Cisco VPN 3000 Concentrators
Remote-Access IPSec Tunnel Without NAC
Remote-Access IPSec Tunnel from an Agentless Client
Remote-Access IPSec Tunnel from a CTA Client
Summary
Review Questions
Chapter 7 Configuring NAC on Cisco ASA and PIX Security Appliances
Architectural Overview of NAC on Cisco Security Appliances
Stateless Failover for NAC
Per-Group NAC Exception List
Configuration Steps of NAC on Cisco Security Appliances
VPN Configuration on the Security Appliances
VPN Configuration on the Cisco VPN Client
NAC Configuration on the Cisco Security Appliances
Testing, Monitoring, and Troubleshooting NAC on Cisco Security Appliances
Remote-Access IPSec Tunnel Without NAC
Remote-Access IPSec Tunnel from an Agentless Client
Remote-Access IPSec Tunnel from a CTA Client
Monitoring of NAC Sessions
Summary
Review Questions
Chapter 8 Cisco Secure Access Control Server
Installing ACS
Installation Prerequisites
Installing ACS on a Windows Server
Upgrading from Previous Versions of ACS Server
Post-Installation Tasks
Initial ACS Configuration
Configuring Network Device Groups (Optional)
Adding Network Access Devices
Configuring RADIUS Attributes and Advanced Options
Installing Certificates
Configuring Global Authentication Protocols
Creating Network Access Profiles Using NAC Templates
Posture Validation
Internal Posture-Validation Policies
External Posture Validation and Audit Servers
Miscellaneous Posture-Validation Options
Posture Enforcement
Downloadable IP ACLs
VLAN Assignment
Policy-Based ACLs
RADIUS Authorization Components
Network Access Profiles
Protocols Policy
Authentication Policy
Posture Validation Policy
Authorization Policy
Network Access Filtering
NAC Agentless Hosts
Centralized Agentless Host Policy for NAC-L3-IP and NAC-L2-IP
Centralized Agentless Host Policy for NAC-L2-802.1X (MAC Authentication Bypass)
Configuring the Agentless Host Policy on ACS
User Databases
Importing Vendor Attribute-Value Pairs
Enabling Logging
Configuring Failed Attempts Logging
Configuring Passed Authentications Logging
Configuring RADIUS Accounting Logging
Replication
Troubleshooting ACS
Enabling Service Debug Logging
Invalid Protocol Data
RADIUS Posture-Validation Requests Are Not Mapped to the Correct NAP
RADIUS Dictionaries Missing from the Interface Configuration Section
Certificate Issues—EAP-TLS or PEAP Authentication Failed During SSL Handshake in Failed Attempts Log
Summary
Review Questions
Chapter 9 Cisco Security Agent
Cisco Security Agent Architecture
CSA MC Rule Definitions
Global Event Correlation
Installing Cisco Security Agents Management Center
Configuring CSA NAC-Related Features
Creating Groups
Creating Agent Kits
System State and NAC Posture Changes
Summary
Review Questions
Chapter 10 Antivirus Software Integration
Supported Antivirus Software Vendors
Antivirus Software Posture Plug-Ins
Antivirus Policy Servers and the Host Credential Authorization Protocol (HCAP)
Adding External Antivirus Policy Servers in Cisco Secure ACS
Summary
Review Questions
Chapter 11 Audit Servers
Options for Handling Agentless Hosts
MAC Authentication Bypass
Audit Servers
Cisco Network Admission Control Agent Software For Mac Osx
Architectural Overview of NAC for Agentless Hosts
Configuring Audit Servers
Installation of QualysGuard Scanner Appliance
Configuration of QualysGuard Scanner Appliance
Configuration of CS-ACS Server
Monitoring of Agentless Hosts
Monitoring Agentless Hosts on QualysGuard Scanner
Monitoring CS-ACS Logs
Monitoring Agentless Hosts on a Cisco NAD
Summary
Review Questions
Chapter 12 Remediation
Altiris
Altiris Network Discovery
Importing Attribute Files to Cisco Secure ACS
Setting External Posture Validation Audit Server on Cisco Secure ACS
Installing the Altiris Network Access Agent and Posture Plug-In
Exception Policies

Creating Posture Policies on the Altiris Notification Server
PatchLink
Summary
Review Questions
Part III Deployment Scenarios
Chapter 13 Deploying and Troubleshooting NAC in Small Businesses
NAC Requirements for a Small Business
Small Business Network Topology
Configuring NAC in a Small Business
Cisco Secure ACS
End-User Clients
Switches
Web Server
Troubleshooting NAC Deployment in a Small Business
show Commands
EAP over UDP Logging
Cisco Secure ACS Logging
Certificate Issues: EAP-TLS or PEAP Authentication Failed During SSL Handshake
Incorrect Time or Date
Summary
Review Questions
Chapter 14 Deploying and Troubleshooting NAC in Medium-Size Enterprises
Deployment Overview of NAC in a Medium-Size Enterprise
The User Network
The Management Network
The Quarantine Network
Business Requirements for NAC in a Medium-Size Enterprise
Medium-Size Enterprise NAC Solution Highlights
Enforcement Actions
Steps for Configuring NAC in a Medium-Size Enterprise
Catalyst 6500 CatOS Configuration
VPN 3000 Concentrator Configuration
Audit Server Configuration
Altiris Quarantine Solution Configuration
Trend Micro Policy Server Configuration
Cisco Secure ACS Configuration
CSA-MC Server Configuration
End-User Clients
Monitoring and Troubleshooting NAC in a Medium-Size Enterprise
Diagnosing NAC on Catalyst 6500 Switch
Diagnosing NAC on a VPN 3000 Concentrator
Cisco Secure ACS Logging
Summary
Review Questions
Chapter 15 Deploying and Troubleshooting NAC in Large Enterprises
Business Requirements for Deploying NAC in a Large Enterprise
Security Policies
Enforcement Actions
Design and Network Topology for NAC in a Large Enterprise
Branch Office
Regional Office
Headquarters
Configuring NAC in a Large Enterprise
ACS
End-User Clients
Switches
Troubleshooting NAC Deployment in a Large Enterprise
show Commands
debug Commands
ACS Logs and CS-MARS
Summary
Network Admission Control
NAC: Phase I
NAC: Phase II
NAC Program Participants
Components That Make Up the NAC Framework Solution
Cisco Trust Agent
Cisco Security Agent
Network-Access Devices
Cisco VPN 3000 Series Concentrator
Cisco Secure Access Control Server
Event Monitoring, Analysis, and Reporting
Summary
Review Questions
Part II Configuration Guidelines
Chapter 2 Cisco Trust Agent
Preparing for Deployment of CTA
Supported Operating Systems
Deploying CTA in a Lab Environment
CTA Windows Installation
CTA Windows Installation with the 802.1X Wired Supplicant
CTA Mac Installation
CTA Linux Installation
Installing the CA Certificate
User Notifications
Customizing CTA with the Optional ctad.ini File
[main] Section
[EAPoUDP] Section
[UserNotifies] Section
[ServerCertDNVerification] Distinguished Name-Matching Section
[Scripting_Interface] Section
Example ctad.ini
CTA Scripting Interface
Requirements for Using the Scripting Interface
Executing the Scripting Interface
CTA Logging Service
Creating a ctalogd.ini File
Using the clogcli Utility
Deploying CTA in a Production Network
Deploying CTA on Windows
Deploying CTA on Mac OS X
Deploying CTA on Linux
Troubleshooting CTA
Installation Issues
Communication Issues
System Logs
CTA Client Fails to Receive a Posture Token
CTA 802.1X Wired Client
Client Is Disconnected (Suspended)
Chapter Summary
References
Review Question
Chapter 3 Cisco Secure Services Client
Installing and Configuring the Cisco Secure Services Client
Minimum System Requirements
Installing the Cisco Secure Services Administrative Client
Configuring the Cisco Secure Services Administrative Client
Deploying the Cisco Secure Services Client in a Production Network
End-User Client Deployment Installation Prerequisite
Creating End-User Client-Configuration Files
Creating the License File
Deploying the End-User Client
Viewing the Current Status of the Cisco Secure Services Client
Windows Wireless Zero Configuration
Troubleshooting the Cisco Secure Services Client
System Report Utility
Viewing the Client Logs and Connection Status in Real Time
Client Icon Does Not Appear in System Tray
Client GUI Does Not Start
Client Does Not Prompt for Password
Wireless Client Is Immediately Dissociated after 802.1X Authentication
Client Is Disconnected (Suspended)
Summary
References
Review Question
Chapter 4 Configuring Layer 2 NAC on Network Access Devices
NAC-L2-IP
Architecture of NAC-L2-IP
Configuring NAC-L2-IP
Troubleshooting NAC-L2-IP
NAC-L2-802.1X
Architecture of NAC-L2-802.1X
Configuring NAC-L2-802.1X
MAC Authentication Bypass
Troubleshooting NAC-L2-802.1X
Configuring NAC-L2-802.1X on Cisco Wireless Access Points
Summary
Review Questions
Chapter 5 Configuring Layer 3 NAC on Network Access Devices
Architectural Overview of NAC on Layer 3 Devices
Configuration Steps of NAC on Layer 3 Devices
Step 1: Configuring AAA Authentication
Step 2: Defining the RADIUS Server
Step 3: Specifying the Interface Access Control List
Step 4: Configuring the NAC Parameters
Step 5: Defining the NAC Intercept Access Control List (Optional)
Step 6: Setting Up the Exception Policies (Optional)
Step 7: Configuring the Clientless Host Parameters (Optional)
Step 8: Optimizing the NAC Parameters (Optional)
Monitoring and Troubleshooting NAC on Layer 3 Devices
Useful Monitoring Commands
Troubleshooting NAC
Summary
Review Questions
Chapter 6 Configuring NAC on Cisco VPN 3000 Series Concentrators
Architectural Overview of NAC on Cisco VPN 3000 Concentrators
Cisco Software Clients
Microsoft L2TP over IPSec Clients
Configuration Steps of NAC on Cisco VPN 3000 Concentrators
VPN Configuration on the VPN 3000 Concentrator
VPN Configuration on the Cisco VPN Client
NAC Configuration on the VPN 3000 Concentrator
Testing, Monitoring, and Troubleshooting NAC on Cisco VPN 3000 Concentrators
Remote-Access IPSec Tunnel Without NAC
Remote-Access IPSec Tunnel from an Agentless Client
Remote-Access IPSec Tunnel from a CTA Client
Summary
Review Questions
Chapter 7 Configuring NAC on Cisco ASA and PIX Security Appliances
Architectural Overview of NAC on Cisco Security Appliances
Stateless Failover for NAC
Per-Group NAC Exception List
Configuration Steps of NAC on Cisco Security Appliances
VPN Configuration on the Security Appliances
VPN Configuration on the Cisco VPN Client
NAC Configuration on the Cisco Security Appliances
Testing, Monitoring, and Troubleshooting NAC on Cisco Security Appliances
Remote-Access IPSec Tunnel Without NAC
Remote-Access IPSec Tunnel from an Agentless Client
Remote-Access IPSec Tunnel from a CTA Client
Monitoring of NAC Sessions
Summary
Review Questions
Chapter 8 Cisco Secure Access Control Server
Installing ACS
Installation Prerequisites
Installing ACS on a Windows Server
Upgrading from Previous Versions of ACS Server
Post-Installation Tasks
Initial ACS Configuration
Configuring Network Device Groups (Optional)
Adding Network Access Devices
Configuring RADIUS Attributes and Advanced Options
Installing Certificates
Configuring Global Authentication Protocols
Creating Network Access Profiles Using NAC Templates
Posture Validation
Internal Posture-Validation Policies
External Posture Validation and Audit Servers
Miscellaneous Posture-Validation Options
Posture Enforcement
Downloadable IP ACLs
VLAN Assignment
Policy-Based ACLs
RADIUS Authorization Components
Network Access Profiles
Protocols Policy
Authentication Policy
Posture Validation Policy
Authorization Policy
Network Access Filtering
NAC Agentless Hosts
Centralized Agentless Host Policy for NAC-L3-IP and NAC-L2-IP
Centralized Agentless Host Policy for NAC-L2-802.1X (MAC Authentication Bypass)
Configuring the Agentless Host Policy on ACS
User Databases
Importing Vendor Attribute-Value Pairs
Enabling Logging
Configuring Failed Attempts Logging
Configuring Passed Authentications Logging
Configuring RADIUS Accounting Logging
Replication
Troubleshooting ACS
Enabling Service Debug Logging
Invalid Protocol Data
RADIUS Posture-Validation Requests Are Not Mapped to the Correct NAP
RADIUS Dictionaries Missing from the Interface Configuration Section
Certificate Issues—EAP-TLS or PEAP Authentication Failed During SSL Handshake in Failed Attempts Log
Summary
Review Questions
Chapter 9 Cisco Security Agent
Cisco Security Agent Architecture
CSA MC Rule Definitions
Global Event Correlation
Installing Cisco Security Agents Management Center
Configuring CSA NAC-Related Features
Creating Groups
Creating Agent Kits
System State and NAC Posture Changes
Summary
Review Questions
Chapter 10 Antivirus Software Integration
Supported Antivirus Software Vendors
Antivirus Software Posture Plug-Ins
Antivirus Policy Servers and the Host Credential Authorization Protocol (HCAP)
Adding External Antivirus Policy Servers in Cisco Secure ACS
Summary
Review Questions
Chapter 11 Audit Servers
Options for Handling Agentless Hosts
MAC Authentication Bypass
Audit Servers
Cisco Network Admission Control Agent Software For Mac Osx
Architectural Overview of NAC for Agentless Hosts
Configuring Audit Servers
Installation of QualysGuard Scanner Appliance
Configuration of QualysGuard Scanner Appliance
Configuration of CS-ACS Server
Monitoring of Agentless Hosts
Monitoring Agentless Hosts on QualysGuard Scanner
Monitoring CS-ACS Logs
Monitoring Agentless Hosts on a Cisco NAD
Summary
Review Questions
Chapter 12 Remediation
Altiris
Altiris Network Discovery
Importing Attribute Files to Cisco Secure ACS
Setting External Posture Validation Audit Server on Cisco Secure ACS
Installing the Altiris Network Access Agent and Posture Plug-In
Exception Policies
Creating Posture Policies on the Altiris Notification Server
PatchLink
Summary
Review Questions
Part III Deployment Scenarios
Chapter 13 Deploying and Troubleshooting NAC in Small Businesses
NAC Requirements for a Small Business
Small Business Network Topology
Configuring NAC in a Small Business
Cisco Secure ACS
End-User Clients
Switches
Web Server
Troubleshooting NAC Deployment in a Small Business
show Commands
EAP over UDP Logging
Cisco Secure ACS Logging
Certificate Issues: EAP-TLS or PEAP Authentication Failed During SSL Handshake
Incorrect Time or Date
Summary
Review Questions
Chapter 14 Deploying and Troubleshooting NAC in Medium-Size Enterprises
Deployment Overview of NAC in a Medium-Size Enterprise
The User Network
The Management Network
The Quarantine Network
Business Requirements for NAC in a Medium-Size Enterprise
Medium-Size Enterprise NAC Solution Highlights
Enforcement Actions
Steps for Configuring NAC in a Medium-Size Enterprise
Catalyst 6500 CatOS Configuration
VPN 3000 Concentrator Configuration
Audit Server Configuration
Altiris Quarantine Solution Configuration
Trend Micro Policy Server Configuration
Cisco Secure ACS Configuration
CSA-MC Server Configuration
End-User Clients
Monitoring and Troubleshooting NAC in a Medium-Size Enterprise
Diagnosing NAC on Catalyst 6500 Switch
Diagnosing NAC on a VPN 3000 Concentrator
Cisco Secure ACS Logging
Summary
Review Questions
Chapter 15 Deploying and Troubleshooting NAC in Large Enterprises
Business Requirements for Deploying NAC in a Large Enterprise
Security Policies
Enforcement Actions
Design and Network Topology for NAC in a Large Enterprise
Branch Office
Regional Office
Headquarters
Configuring NAC in a Large Enterprise
ACS
End-User Clients
Switches
Troubleshooting NAC Deployment in a Large Enterprise
show Commands
debug Commands
ACS Logs and CS-MARS
Summary
Review Questions
Part IV Managing and Monitoring NAC
Chapter 16 NAC Deployment and Management Best Practices
A Phased Approach to Deploying NAC Framework
Readiness Assessment
Stakeholders
Initial Lab Environment
Test Plans
Initial Tuning
Final Deployment Strategy
Provisioning of User Client Software
CSA Management
Maintaining NAC Policies
Keeping Operating System Policies Up-to-Date
Keeping Your Antivirus Policies Up-to-Date
Maintenance of Remediation Servers and Third-Party Software
Technical Support
Education and Awareness
End-User Education and Awareness
Help-Desk Staff Training
Engineering and Networking Staff Training
Summary
References
Review Questions
Chapter 17 Monitoring the NAC Solution Using the Cisco Security Monitoring, Analysis, and Response System
CS-MARS Overview
Setting Up Cisco IOS Routers to Report to CS-MARS
Defining the Cisco IOS Router as a Reporting Device within CS-MARS
Configuring the Cisco IOS Router to Forward Events to CS-MARS
Setting Up Cisco Switches to Report to CS-MARS
Defining the Cisco Switch as a Reporting Device within CS-MARS
Cisco Network Admission Control Agent Software For Mac 2017
Configuring the Cisco Switch to Forward Events to CS-MARS
Configuring ACS to Send Events to CS-MARS
Defining ACS as a Reporting Device within CS-MARS
Configuring Logging on ACS
Configuring 802.1X NADs in ACS to Report to CS-MARS
Installing the pnlog Agent on ACS
Configuring CSA to Send Events to CS-MARS
Defining CSA-MC as a Reporting Device within CS-MARS
Configuring CSA-MC to Forward Events to CS-MARS
Configuring VPN 3000 Concentrators to Send Events to CS-MARS
Defining the VPN 3000 Concentrator as a Reporting Device within CS-MARS
Configuring the VPN 3000 Concentrator to Forward Events to CS-MARS
Configuring the Adaptive Security Appliance and PIX Security Appliance to Send Events to CS-MARS
Defining the ASA/PIX Appliance as a Reporting Device within CS-MARS
Configuring the ASA/PIX Appliance to Forward Events to CS-MARS
Configuring QualysGuard to Send Events to CS-MARS
Generating Reports in CS-MARS
NAC Report—Top Tokens
NAC Report—Infected/Quarantine—Top Hosts
NAC Report—Agentless (Clientless) Hosts
Creating Scheduled NAC Reports
Troubleshooting CS-MARS
Events from a Specific Device Are Not Showing Up
Events Are Showing Up from an Unknown Reporting Device
Trouble Discovering a Monitored Device
Summary
Reference
Review Questions
Part V Appendix
Appendix A Answers to Review Questions
1587052253 TOC 11/2/2006
Other Things You Might Like
- Practical Cisco Unified Communications Security
- eBook (Watermarked) $44.79
- CCNP Security Identity Management SISE 300-715 Official Cert Guide Premium Edition and Practice Test
- Premium Edition eBook $55.99
- Cisco Software-Defined Access
- eBook (Watermarked) $38.39
This chapter covers the following topics:
- Introduction to Network Admission Control
- Review of NAC Phase I and Phase II architecture
- Overview of the components that make up the NAC Framework solution, including:
- - Cisco Trust Agent
- - Cisco Security Agent
- - Network-access devices
- - Cisco Secure Access Control Server
- - Event monitoring, correlation, and reporting
One of the biggest challenges corporations face today is securing the internal network. When the words network security are mentioned, most people immediately associate this phrase with protecting their network from external threats. Few people think of the internal threats that already exist. Unpatched end-host systems, out-of-date antivirus signatures, and disabled or nonexistent personal firewalls all weaken the internal security of corporate networks and make them vulnerable to data theft and attacks. Preventing or limiting these hosts' access to the corporate network has been difficult to do until now.
Cisco Systems has launched the Self-Defending Network Initiative (SDNI) to dramatically improve the network's capability to identify, prevent, and adapt to threats. A key part of this initiative is Network Admission Control (NAC). NAC is a multipart solution that validates the security posture of the endpoint before admitting it on the network. If admitted, NAC can also be used to define what resources the endpoint has access to, based on the endpoint's overall security posture.
This chapter is meant to provide you with an overall review of the NAC Framework solution. We start by covering what NAC is and why companies would want to deploy it. Then we cover an architectural overview of the initial NAC solution (NAC Phase I), followed by an architectural overview of the current NAC solution (NAC Phase II). In the remainder of the chapter, we provide an overview of the individual components that make up NAC. Each component has a dedicated chapter in this book where we cover the installation, configuration, and steps to troubleshoot that component in the NAC solution. After reading this chapter, you should be familiar with the concepts and components that make up the NAC Framework and should be ready to start installing and configuring NAC in your network.
If you are unfamiliar with NAC or are interested in learning more about the architecture of the NAC solution, we invite you to read Cisco Network Admission Control, Volume I: NAC Architecture and Design (ISBN 1587052415), published by Cisco Press.
Cisco Network Admission Control Agent Software For Mac Download
Network Admission Control
Reports of data and identity theft have become hot topics in the news recently. Unfortunately, they have also become fairly common, often resulting in millions of dollars' worth of damage to the companies affected. Traditionally, network security professionals have focused much of their time securing the front door to their networked companies—their Internet presence. Stateful firewalls often sit at the gateways, and, in most cases, these are supplemented with inline intrusion-prevention devices (IPS), antivirus scanners, and denial-of-service (DoS) mitigation devices. Behind this virtual fortress of protection sit hardened servers, which serve up the corporate web presence. Many companies are proud of their investment in this type of security and advertise this fact. Now, don't get me wrong—this type of security is important. However, sometimes in the zeal to make the web presence secure, we forget that a huge threat exists from within.
It is becoming mandatory these days for employees to have access to the Internet; often it is a critical component of their jobs. However, have you thought about devices that your employees are using to access the Internet? How secure are they? If they are corporate assets, they should have the corporate antivirus software installed and possibly a personal firewall. But how do you know the employee has not disabled one or more of these and thereby reduced the security of not only the device, but also your internal network, and opened it up to threats?
While you are pondering that thought, let me give you another. How many noncorporate assets connect to your network? How many employees bring in their personal laptop, their personal digital assistant (PDA), or even their cell phone and connect it to the corporate network? What about partners and outside vendors? How much control do you have over these devices? Imagine what could happen if a rootkit or some other Trojan back door was installed on one of these devices and now has access to your internal network. How many confidential documents or corporate secrets could be stolen by attackers within?
It is often easier to consider the mistakes or ignorance of others, but how many times have you been guilty of letting the security of your own PC lapse? How many times have you been notified of a new critical security patch for your laptop or desktop and clicked the Not Now button, choosing instead to install it later? I am sure all of us are guilty of this; I know I am.
Installing security patches, especially to the operating system, usually results in the mandatory reboot. This usually comes at the worst time of the day, when shutting down your applications and rebooting is not an option. So we make a mental note to install the patches when we leave for the day, but how many times do we actually follow through? More often than not, weeks or months could go by before we find the time to install the patches. During this time, the PC remains susceptible to the targeted attack.
Although I have highlighted only a few of the common threats to the internal security of your corporate network, I am sure you can think of many more. Home users connecting via a VPN tunnel, remote sales forces connecting from the local hotspot or hotel, partners with direct site-to-site tunnels to your company—the list goes on. These are the types of threats NAC was designed to protect you against and eliminate.
NAC is a Cisco-led, multivendor initiative focused on eliminating threats to the corporate network caused by insecure endpoints attaching to the network. In its simplest form, NAC defines a set of policies that are used to evaluate the security posture of an endpoint that wants to join the network. The endpoint can be a PC, a PDA, a server, an IP phone, a printer, and so on. Based on the security posture of the endpoint, it can be given unrestricted access to the network—if it meets all the security requirements. Devices that fail to fully satisfy the security requirements can be quarantined where autoremediation ensues. (Remediation servers can automatically push out patches and updates to software running on the endpoints to improve their security posture.) Alternatively, devices can be denied access to the network altogether, or they can be placed in their own VLAN and given limited access to the network. All of these actions are fully configurable, along with the security policy to be enforced.
NAC: Phase I
Cisco rolled out NAC in a series of phases. Phase I was launched in the summer of 2004. It includes using Cisco routers as the enforcement point, running Cisco IOS Release 12.3(8)T or later. When NAC is deployed on Cisco IOS routers, it is called NAC-L3-IP because the router operates at Layer 3 (the IP layer) and contains noncompliant endpoints using Layer 3 Access Control Lists (ACLs). As endpoints attempt to access devices through the router, they are queried to determine their security posture. Based on the endpoint's security posture, a security policy for the endpoint is pushed down to the router that permits or restricts access. Figure 1-1 shows a NAC-L3-IP architecture overview.
Figure 1-1 NAC-L3-IP Architecture Overview
Follow along in Figure 1-1 as we walk through each step of this process:
- The endpoint sends a packet, which passes through the router, on to its destination. The packet matches the Intercept ACL applied to the router's interface, which triggers the NAC-L3-IP posture-validation process.
- The router initiates an EAP over UDP (EAPoUDP) tunnel to the Cisco Trust Agent (CTA) on the endpoint. This is the first part in setting up a secure tunnel between the endpoint and the Cisco Secure Access Control Server (ACS).
- Next, the router initiates a RADIUS tunnel to the Cisco Secure ACS server. This is the second part in establishing a secure tunnel between the endpoint and Cisco Secure ACS.
- With the EAPoUDP and RADIUS tunnels established, the Cisco Secure ACS server establishes a Protected Extensible Authentication Protocol (PEAP) tunnel with the endpoint and queries it for posture credentials. The posture credentials are sent to Cisco Secure ACS using EAP type-length-values (EAP-TLVs). The EAP-TLVs allow for any number of posture credentials to be returned from the end device.
- (Optional) Cisco Secure ACS proxies some of the posture credentials to additional validation servers (in this case, an antivirus server) using the Host Credentials Authorization Protocol (HCAP).
- Cisco Secure ACS analyzes the end host's security posture by passing the posture credentials through rules, defined by the administrator in Cisco Secure ACS, or by sending them to external posture-validation servers. The host is then assigned an overall security posture, based on those results. The overall security posture is then forwarded to the router, along with the associated access list, which restricts the host's access to the network, based on its security posture.
- (Optional) Cisco Secure ACS can also send a message to the endpoint, which, in turn, is displayed to the user to provide notification about the security posture of the host. Cisco Secure ACS can also redirect the user's browser to a remediation server, where patches and updates can be applied.
- If the host is deemed 'healthy' (its security posture meets the requirements of the company), it is permitted to access the network unrestricted.
The protocols used in Figure 1-1 are discussed in more detail in later chapters. For now, it is important to know only that the posture credentials and security policy are carried over authenticated and encrypted tunnels for added security. Figure 1-2 illustrates the relationship among these protocols in a graphical way. The PEAP-encrypted tunnel is carried over both the RADIUS and EAPoUDP tunnels. It contains the EAP-TLVs used to determine the host's posture.
Figure 1-2 Graphical Representation of Protocols Used in Phase I NAC
NAC: Phase II
Cisco launched NAC Phase II in the summer of 2005. Phase II expands on Phase I by placing NAC capabilities into several more product lines, including the Catalyst line of switches, the VPN 3000 series concentrators, the ASA 5500 series and PIX 500 series security appliances, the Aironet wireless access points, and the Wireless LAN Service Module. With these new additions, the enforcement point has moved to the network edge, providing enforcement and containment at a port (or host) level instead of at the gateway. These additions also created some new terminology:
NAC-L2-IP—The term NAC-L2-IP is used when NAC is applied to a Catalyst switch, on a per-port basis. You can think of NAC-L2-IP as being identical to NAC-L3-IP, but the enforcement policy is an IP-based ACL applied to a switch port instead of a routed port. Likewise, the protocol flow as defined in Figure 1-1 is the same for NAC-L2-IP.
One other difference between NAC-L2-IP and NAC-L3-IP is that, in NAC-L2-IP, the posture assessment is triggered when the switch port receives a Dynamic Host Configuration Protocol (DHCP) packet or an Address Resolution Protocol (ARP) packet from the endpoint attempting to connect to the network. Then the switch establishes the EAPoUDP tunnel to the endpoint to start the posture-validation process.
NAC-L2-802.1X—The term NAC-L2-802.1X is used when NAC is applied to a switch port along with 802.1X authentication. 802.1X provides for both user- and machine-based authentication of the endpoint before the switchport forwards any traffic to the network. NAC-L2-802.1X adds security posturing to 802.1X by way of the Extensible Authentication Protocol–Flexible Authentication via Secure Tunneling (EAP-FAST) protocol. Thus, the posture credentials are carried through EAP-FAST over a Transport Layer Security (TLS) tunnel from the endpoint directly to Cisco Secure ACS. Consequently, an 802.1X supplicant that supports EAP-FAST is needed for NAC-L2-802.1X.
When NAC-L2-802.1X is enabled and a PC is connected to a switch port, 802.1X authentication and posture validation occur within the same EAP transaction. The posture credentials are included within the EAP-FAST messages that are transmitted on top of the 802.1X protocol. However, unlike NAC-L3-IP and NAC-L2-IP, posture enforcement is done not through ACLs but instead solely through VLAN assignment.
Figure 1-3 illustrates NAC-L2-802.1X on a switch that uses 802.1X authentication as the Layer 2 protocol.
Follow along in Figure 1-3 as we walk through the process of what happens when an endpoint connects to a switch with NAC-L2-802.1X enabled on the port:
- The end device is attached to a switch port.
- As the link comes up, the client's 802.1X supplicant initiates an authentication request with the switch via 802.1X.
- The user's (or machine's) credentials are sent from the switch to the Cisco Secure ACS server via RADIUS.
- The Cisco Secure ACS server authenticates the user (or machine).
- CTA and Cisco Secure ACS now establish an EAP-FAST tunnel over the existing 802.1x and RADIUS sessions.
- The Cisco Secure ACS server queries CTA for posture credentials using the EAP tunnel.
- (Optional) Cisco Secure ACS optionally proxies some of the posture credentials to additional validation servers (in this case, an antivirus server) using HCAP. These validation servers can notify the agents on the endpoint and trigger their own updates.
- Cisco Secure ACS applies the security policy to the retrieved posture credentials, and the host is assigned an overall posture. This security posture is forwarded to the switch along with the associated VLAN to be applied to the port the host is connected to.
- (Optional) Based on the posture credentials, Cisco Secure ACS can send a message to the end host to be displayed to the user or can redirect the browser to a remediation server. The remediation server can automatically push out patches and updates to the endpoint to bring it in compliance with the corporate security policy.
- The host is now permitted (or denied) access to the network, based on its posture and the VLAN it is assigned to.
Periodic Revalidation
Periodic revalidations are built into the NAC-L3-IP and NAC-L2-IP solution. The network-access device (NAD) initiates the process by periodically polling validated endpoints to determine whether a change has been made in their posture. CTA alerts the NAD of any changes on the end host, and the NAD then issues a full revalidation and posture assessment.
This security measure prevents users from validating their host and then lowering their security posture after they have been granted access to the network.
Additionally, a separate revalidation timer requires all active hosts to be fully revalidated every 30 minutes, by default. This enables the network administrator to change the security policy on the fly. All already-validated end hosts must meet this new policy when their revalidation timer expires. The following example further illustrates this point:
Bob, the network administrator of example.com, receives a new alert about a critical security vulnerability in Microsoft Windows. Realizing the security impact that this vulnerability might have on his network, Bob immediately modifies his NAC security policy to require the hotfix that addresses this vulnerability to be applied on all end hosts on his network. Because it is during the day, most users validated their machines on the network when they arrived in the morning. Without periodic revalidation, Bob would have to wait until each user disconnects and reconnects to the network before the endpoint is revalidated. However, the revalidation timer solves this by requiring all active, validated hosts to be fully revalidated every 30 minutes (by default).
NAC Agentless Hosts
A NAC agentless host (NAH) (or a clientless endpoint) is a device that does not have CTA installed. Therefore, it cannot respond to the EAPoUDP or EAP-FAST request from the NAD. A printer, a webcam, an IP phone, and a guest PC are all examples of NAHs.
Individual policies can be defined on the NAD for NAHs. The policy can be designed to exclude a specific MAC or IP address or a range of addresses. Alternatively, a global policy can be defined on Cisco Secure ACS for NAHs. After the EAPoUDP or EAP-FAST session times out, the NAD can notify Cisco Secure ACS of the NAH, and Cisco Secure ACS can apply the appropriate authorization rights. We look at NAHs in more detail in Chapters 4, 'Configuring Layer 2 NAC on Network-Access Devices,' through 8, 'Cisco Secure Access Control Server.'
Another option for NAHs (which is part of NAC Phase II) is to use an audit server to scan the host for the services running on it and potential vulnerabilities. Cisco Secure ACS instructs the audit server on which hosts to scan by using the Generic Authorization Message Exchange (GAME) protocol. When the scan is complete, the audit server returns the results to Cisco Secure ACS through the GAME protocol, and Cisco Secure ACS uses these results to apply a security posture and overall policy to the end host.
NAC Program Participants
Cisco Systems leads the NAC program, but is open to any vendor that wants to participate. To ensure interoperability, Cisco requires all vendors shipping NAC-enabled code to have it tested either by an independent third-party testing center or by Cisco Systems. At the time of publication, more than 75 vendors were enrolled in the NAC program. A current list of program participants is maintained by Cisco at http://www.cisco.com/web/partners/pr46/nac/partners.html.

